What Are The Steps Of The Information Security Program Lifecycle?
Last Updated on 5 months by Touhid
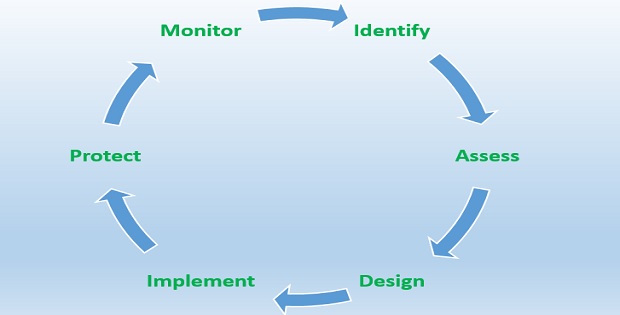
Do you know? What are the steps of the information security program lifecycle? The steps of the information security program lifecycle identify, assess, design, implement, protect, and monitor.
The information security program life cycle ensures the security of sensitive information, business data, and IT assets from unauthorized access.
Table of Contents
What Are the Steps of The Information Security Program Lifecycle?
In today’s cyber world, information security plays an important role in our daily lives, such as personal, business, agency, or government offices. The steps of the information security program life cycle define the method of reducing the security risk of your information and IT assets. The information security program life cycle is important to protect the sensitive data of an organization and a country.
Now, what are the steps of the information security program lifecycle? There are several steps in the information security program lifecycle, which are as follows:
- Identify
- Assess
- Design
- Implement
- Protect
- Monitor
Overview: Steps Of the Information Security Lifecycle
Step 1: Identify
Identifying is the first step of the information security program lifecycle which determines what types of information or data need to be secured. If you don’t have the correct information about your data or materials, then you can’t properly secure your data and documents.
In this step of the information security program lifecycle, initially, you should identify what types of information need to be secured or protected from unauthorized access.
So, you have to be acquainted with your network architecture, identify the number of servers, and what types of applications software are running on which server.
However, some key queries of the identification steps are as follows:
- Number of hardware devices such as servers, routers, and switches.
- Which types of operating systems running on your server, such as Windows, Linux, and UNIX?
- What types of applications or software are running on the server?
- What types of information are important to your organization?
- What types of assets or materials are top priority?
- Are the applications or software secured from cyber security threats?
- Server room or data center is restricted from unauthorized access?
- Is there cyber security tools on your system such as a firewall, and web application firewall (WAF)?
An IT audit team should involve your organization on a permanent (internal audit team) or contractual basis to answer the above queries. They will analyze and assess your ICT infrastructure, and interview and discuss with your security professionals, IT staff, and employees who are working in this section.
There are also security testing tools called Network Mapper or Nmap, which is an open-source penetration testing tool. It is used for network discovery and identifying information about applications and operating systems. The tool is used by the system or network administrators of an organization.
Learn more about Network Penetration tools Nmap.
Step 2: Assess
Assessment is the second step of the information security program lifecycle which takes the information from identification steps. In this assessment step, the security professionals will perform a security assessment or evaluation of the company’s assets.
The assessment steps are the most important and extensive steps of the information security program lifecycle. Typically, it will cover system reviews, server reviews, and vulnerability assessments of each system.
System reviews
System reviews or ICT structure reviews of an organization are the first steps of the assessment process. The security professionals will check the overall system such as software types, warnings, security measures, and outdated software versions, and gather additional information to discover vulnerabilities.
Server Review
Security specialists will collect the required information on each server and check the server configurations such as RAM size, hard disk space, processor, operating system, and license version. The team will evaluate the User IDs, password policies, login protocols, and remote accessibility of each server. The security team will also check server settings and find out the problems of each server.
Vulnerability assessments
After completion of system and server reviews, the security team will take action for a vulnerability assessment of each system. The security team will emphasize the most important systems (such as stores of sensitive information), where security breaches can happen.
In vulnerability assessment steps, the team will identify existing security risks, preventive measures for risks or threats, data security, future security threats, and the capability to handle new threats.
Learn more about vulnerability assessments or penetration testing software.
Step 3: Design
Design is the third steps of the information security program lifecycle. The security team will take the necessary action to solve the problems of assessment steps such as security risks, data breaches, cyber threats, and complications, which are also identified in the assessment steps.
The security team will design a solution based on the collected information and requirements. The team will consider the following issues during the design phase to ensure system availability.
Accessibility or Continuity
The design should ensure system accessibility in case of natural disaster system crash or any other reason. In that case, the team should design the system for hosting both primary and secondary servers. The secondary server (system backup) will perform and ensure business continuity in case of disaster or down of the primary server.
System Security
Security is an important issue for every business organization to prevent cyber thefts and security risks. The security team should consider the security measures to ensure the organization’s reputation.
Here, we have mentioned some reasons why security is important for an organization, which are as follows:
- To secure organization information and documents.
- To protect computer systems from cyber threats.
- To keep the organization’s reputation.
- To increase business revenues.
- To reduce vulnerabilities and
- Ensure data availability and accessibility.
So, the security team designed the system based on several security layers. There are different types of cyber security tools and techniques, which can ensure security, such as authentication, firewall, web application firewall, SSL certificate, encryption, and antivirus software.
Learn more about Cyber Security Tools.
What are the steps of the information security program lifecycle? There are six steps of the information security program lifecycle that we have mentioned above. Already, four steps have been discussed. Now, we will discuss another important step in the information security program lifecycle, which is implementation.
Step 4: Implementation
After completion of the design phase, the next steps of the information security life cycle is implementation. Now, the team will start implementation work on the approved design. The team will create an implementation or deployment strategy for the solution. The implementation strategy or plan can include the following aspects:
Develop an Effective Plan
First, the security team will develop an effective step-by-step change plan. The change plan should have an option for any employee of the organization to receive professional training on new processes to implement the system.
A system may have the most important and least important segments. In this case, the team will emphasize the most important portions and work down toward the least vulnerable portions.
Assign Roles and Responsibilities
To implement the change plan, the security team will assign individual roles and responsibilities to team members such as managers, IT team leaders, and other team members.
Resource Collection
Now, the team will collect the required resources and tools such as software, hardware devices, computer networking, and security software in order to deploy the change plan.
Testing
The security team will evaluate and test the change plan during implementation steps and the team will look after the new changes and ensure the change plan has been completed.
Step 5: Protect
The protection steps of the information security program lifecycle are very significant which ensures that the system is secured. This step ensures that your system has been followed and implemented according to security rules and techniques.
The security team will review the complete system to ensure that the system has been implemented correctly and functioning properly, the system is free from risk and ensures security.
In this phase, information security teams will also scrutinize any new changes or requirements that have been added during the previous steps and ensure that they have been applied appropriately with security guidelines.

Step 6: Monitor
The monitor is the last step of the information security program lifecycle, where the security team will monitor the overall system using monitoring software’s or tools. There are some key functionalities of this steps, which are mentioned as follows:
- Ensure system security and increase security measures for new security threats.
- Identify the risks and vulnerabilities in existing systems or new vulnerabilities when they appear in the system.
- Monitor the system manually or with the help of monitoring software’s.
- Monitor the network infrastructure and check the configuration of hardware devices such as servers, routers, switches, and firewalls.
- Update the operating system, antivirus software, and application software.
- Nowadays, threats are changing their attacking techniques, so increase awareness programs, and workshops on cyber security.
Conclusion
Finally, the main aim of information security is to maintain confidentiality, integrity, and availability of information.
In this post, our security team has discussed about what are the steps of the information security program lifecycle. Hope the article will be helpful for you to learn about the steps of the security program lifecycle.
Affiliate Disclosure : Cyberthreatportal is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for website owners to earn advertising fees by advertising and linking to amazon.com.